Access Control Systems (ACS)
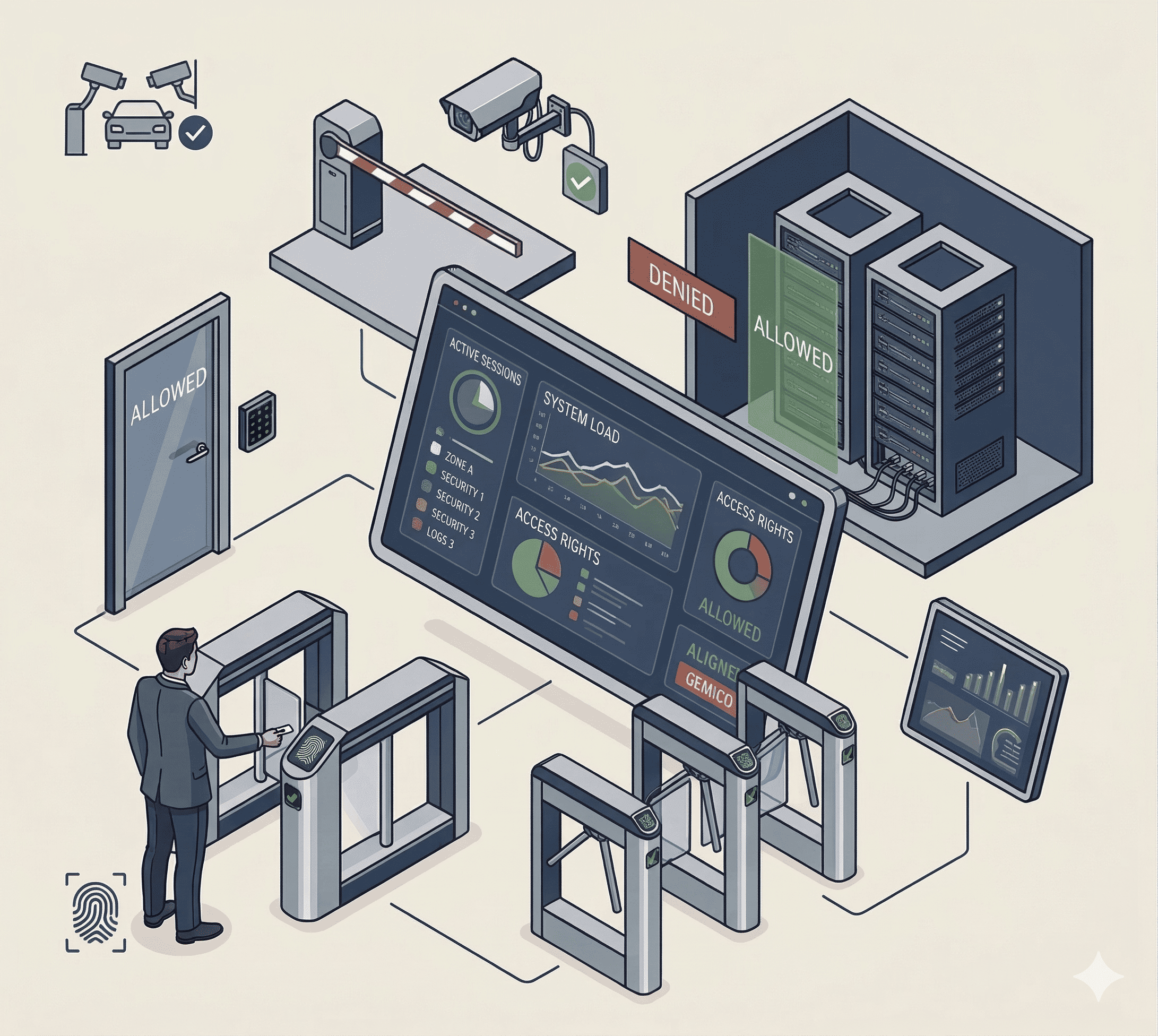
Access Control and Management System (abbreviated ACMS or ACS) — is a complex of technical and software security tools that regulates the entry / exit and movement of people or vehicles in protected areas, for administrative monitoring and prevention of unauthorized access.
An access control system solves the following tasks at an enterprise:
- identification of persons who have, or do not have, access rights;
- access differentiation to various premises;
- management of automatic modes;
- recording of the time a person spends at the facility;
- information processing and statistics management.
Identifiers:
- contactless access cards (proximity cards),
- cards with barcode or QR code media,
- biometric: face, fingerprint, palm print,
- vehicle license plates, wagon numbers.
Structure:
An access control system is typically built using a main controller, additional controllers or expansion modules, and intelligent card readers or biometric identifiers.
Vendors.
The company offers the following manufacturers for ACS design and implementation:
Ukrainian manufacturer U-Prox. Follow the link
https://security.u-prox.systems/u-prox-mpx-en/
German manufacturer Bosch. Follow the link
https://commerce.boschsecurity.com/pl/ru/Access-Control-Systems/c/22458312587
Australian company ICT. Follow the link
https://ict.co/products-solutions/our-solutions/access-control/
Turnstiles and road blockers, bollards:
Ukrainian manufacturer Tiso. Follow the link
https://tiso.global/ua/
Barriers:
Swiss manufacturer Magnetic-access. Follow the link
https://www.magnetic-access.com/en/company/history.html
Features of implemented solutions
The practical features of implemented solutions are:
- Compilation of spatial and time access zones for personnel
- Integration with Active Directory
- Development of pass layouts that allow simultaneous use of paper and electronic media
- Entry and printing of codes on cards in accordance with the requirements of Security Departments of military enterprises
- Card copy protection
- Issuance of electronic passes for personnel and vehicles
- Report generation in accordance with the requirements of HR Departments, security bureaus, accounting departments, etc.
- Encryption of data transmission channels between controllers
Equipment and operating principle
Information about the visitor (contactless card, key fob, fingerprints, retina pattern, vehicle number, etc.) is read by a special device (the type depends on the identifier type, typically a Proximity reader) and transmitted to the controller for further processing.
The controller makes decisions on granting or denying access based on the received data. Depending on the type of system, the controller can operate autonomously or in conjunction with others under the control of a master computer. The received information is stored in the system memory for further use: compiling reports, statistics, time tracking, and for managing actuators: locks, barriers, turnstiles, blockers, bollards, etc.




